I configured Wireguard VPN.
The client can connect via VPN and gets the right IP address (he one I configured in the peers).
When connected I can not reach my LAN. A traceroute to an IP of a server in my LAN shows that the traffic does not go over the VPN adapter but straight to my default gateway and internet.
Do I have to add another thing before the Wireguard VPN to work?
When I login I cant ping
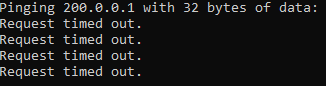
200.0.0.1 is the gateway of the network.
200.0.0.10 is the application server.
Reply
I tested on local protector and it all seems working fine. In any case, better add specific firewall rules for interface wg0, a new zone and new default policies. .
Then I've tested connecting to IP:51820 and it doesn't work. On the Protector, I have activated a tcpdump, but it's like there's no UDP traffic on port 51820. This is what it should show in a normal case:
Wireguard uses UDP as its transport protocol, so the first thing to check is if port 51820/UDP has been forwarded from the public IP to the local protector IP 200.0.0.254.
To check if the connection has been established, it's better try pinging 10.0.0.1, because the Protector vpn is set to accept packets in this ip range: 10.0.0.0/24
If they want to see the protector network 200.x : of course, the traffic from their clients to the protector network 200.0.0.0/24 must be routed through the vpn tunnel. To do so, they have 2 options:
1- Add a static routing on their clients, so that all traffic that must go to 200.x goes through 10.x (route add…. on the command prompt)
2- Route ALL the traffic of their clients to the VPN tunnel. To do so, they have to configure their wireguard clients with AllowedIPs=0.0.0.0/0, and enable the Kill-switch checkbox at the bottom, like in the picture.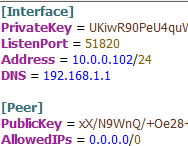
Comments
0 comments
Please sign in to leave a comment.